Recently we published results from the hacking challenge on our website which was online since 2021 when we started using wordpress. To use wordpress is interesting from the security point of view, because it is clearly the “most wanted” CMS by adversaries.
Some weeks ago we “raised the bar” and applied the professional feed of wordfence on our website to make it more resilient agains adversaries of all knowledge levels. We try to limit the attack surface but on one day or another we expect to get an intrusion. The wordfence plugin has visuals in place and it sends alerts to the administrator but:
- the website administrator should not be responsible for security monitoring (separation of concerns).
- it is safe to assume that an attacker who is able to compromise the website will be able to switch off wordfence alerts to the administrator.
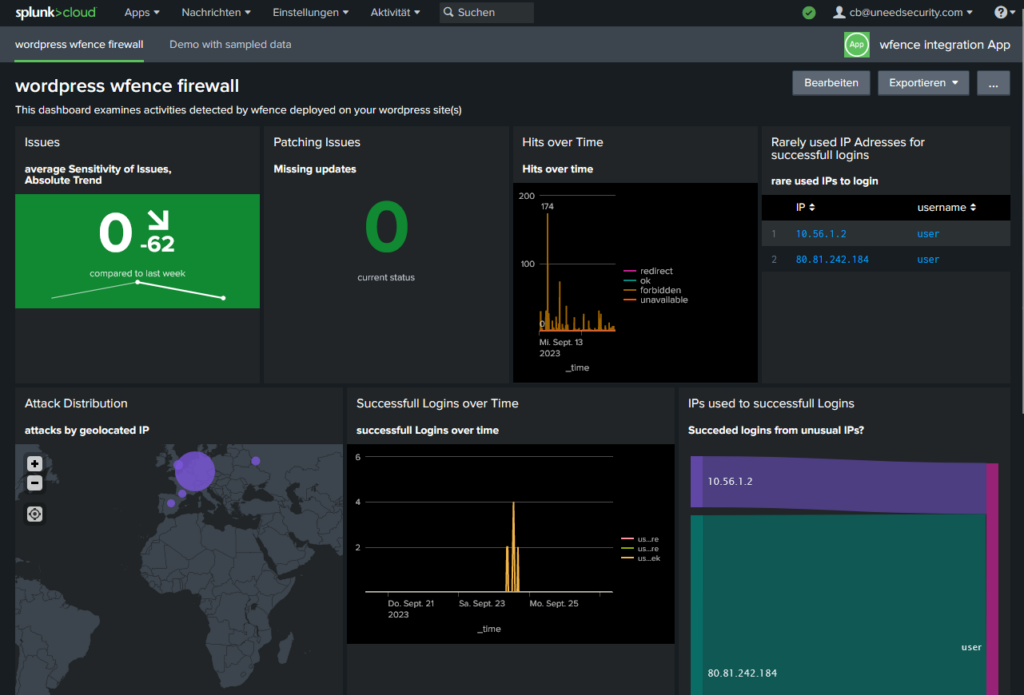
So it is better to integrate the attack information into our comprehensive SIEM as soon as they are detected by wfence.
But before you see them in nice dashboards there are some efforts necessary. First we could not easily install the splunk universal forwarder, because the website is operated as a managed service. Second, wordfence does not have any kind of logging customization. So we had a look into the database structure to understand where the gathered information is stored.
The wfence feature to detect changed files is so relevant! You are alerted already when not much damage occurred. When we analysed the wfence behaviour in an attack we saw that by default only (potentially malicous) changes of files are alerted only in the wp-admin subdirectory. The ordinary user will not be aware of…
Long story short – we build a python skript which picks the interesting news out of the database and uses splunk HEC to forward it to splunk cloud. There it is presented by a splunk app which shows the relevant things with the idea in mind, that we might have intrusions that even wordfence will not recognize. All the source are published on https://gitlab.com/splunk-apps-uns/wfence and the wfence app is on splunkbase.